Top 10 Dangerous DNS Attacks Types and The Prevention Measures
DNS is the acronym used for Domain Name System. It remains under constant attacks. As the threats are multiplying, similarly, there’s no end to the growth in the number of attacks on DNS.
DNS has long been the target of attackers. They always look for swapping away some of the personal data. Thus, the conditions are worsening day by day.
The average costs correlated with DNS mugging rose by 49%, as per the IDC’s research. Also, the average DNS price has trimmed out to be more than $1.27 million.
DNS attacks are becoming more complicated day by day. The number of attacks is rapidly increasing and running from the internal networks. The complex attack pushed the organizations to use a wide range of tools to cope with insider threats.

Indian Cyber Security Solutions works in granting the best Web Penetration Testing Service, Mobile App Penetration Testing Service and Network Penetration Testing Service to corporate organisation Safeguarding their data while utilising it and transferring of it from one person to another. Cyber security is not only a concern for the top management of the enterprises but should also be a high priority for the professionals working in the organization dealing with critical information and intellectual assets of the company. We have been expert in the field of Cyber Security since our inception, having worked for many reputed clients of Private organisation, Public Sector Organisation, Government Organisation as well as for E-Commerce Organisations.
Here now, we will have a glance over the top 10 DNS attack types and will also look for their possible solutions.
- DNS Cache Poisoning Attack
- Distributed Reflection Denial of Service (DRDoS)
- DNS Hijacking
- Phantom Domain Attack
- TCP SYN Floods
- Random Subdomain Attack
- DNS Tunneling
- DNS Flood Attack
- Domain Hijacking
- Botnet-based Attacks

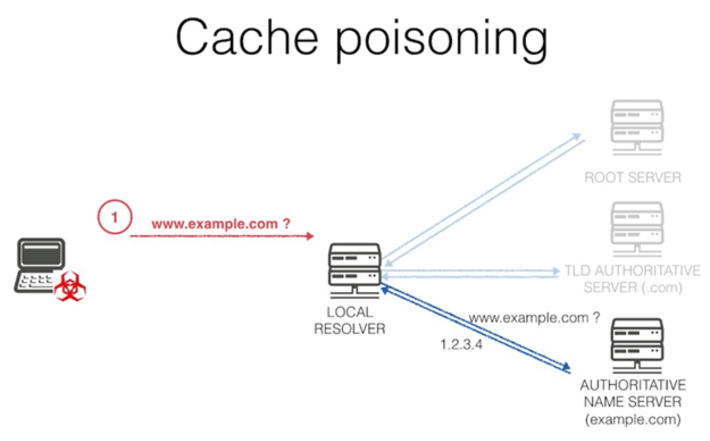
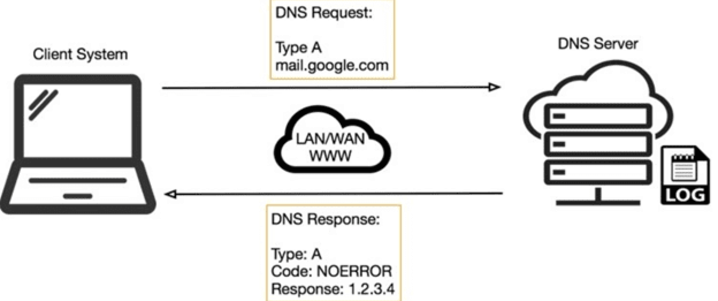
- DNS Cache Poisoning Attack
Cache poisoning, a type of attack that is seen very frequently. The main aim of this attack is to divert web users to some scam websites.
Now, DNS is becoming poisoned rapidly and more usually. It’s not the gmail.com page that is exposed. Instead, it’s a scam page traditionally created by the criminal/hackers where they demand user information to access the website and later use this information to access the user’s personal information. For example, to reclaim the email box accesses. Thus, the users need to be extra careful while accessing any incorrect domain name websites.
This method is an excellent method used by hackers for stalling crucial user information. Cybercriminals use phishing techniques for grabbing out such information. Identification information or credit card information are also taken away. Such attacks are devastating because of the crucial DNS poisoning impact.
- How to Prevent?
There are several methods to solve or prevent this attack.
- The IT teams should configure DNS servers to rely significantly less on trust relations with other DNS servers.
- A few other methods to prevent cache poisoning attacks, as an IT team should configure their DNS name servers:-
- To restrict recursive queries.
- To store only data associated with the requested domain.
- To restrict query responses to only given information about the demanded domain.
- Some cache poisoning tools are even accessible to help many organizations in preventing cache poisoning outbreaks. One of the famous cache poisoning prevention tool is the DNSSEC (Domain Name System Security Extension).
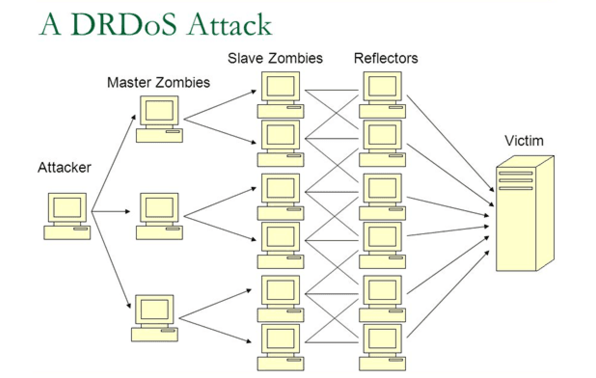
- Distributed Reflection Denial of Service (DRDoS)
Distributed reflective denial of service (DRDoS) attacks concentrate mainly on dragging down the availability of an asset. This is done for the authoritative volume of UDP acknowledgements.
They demand a parodied source IP, with the purpose of a more extensive acknowledgement being transferred to the host, who indeed continues at the forged address.
UDP (User Datagram Protocol) is s protocol used for different choices for a variety of attacks. The reason being it does not build a connection state.
Regulating such attacks at a proper scale makes the idea of shared reflection clear. As the response packs start appearing, the goal experiences a loss of availability.
- How to Prevent?
Preparation for DDoS attacks in advance is always advisable to all organizations as it is exceedingly harder to answer after an attack. DDoS attacks can’t be stopped. The following steps can help in scattering organizational assets.
- Locate the servers in different data centres.
- Assure that the data centres are located on various networks.
- Asure that data centres have several paths.
- Ensure that the data centres, or the networks that the data centres are related to, have no essential security holes or single points of failure.
An organization that highly relies on servers and Internet port are highly essential to ensure that devices are geographically scattered and not located in a particular data centre.
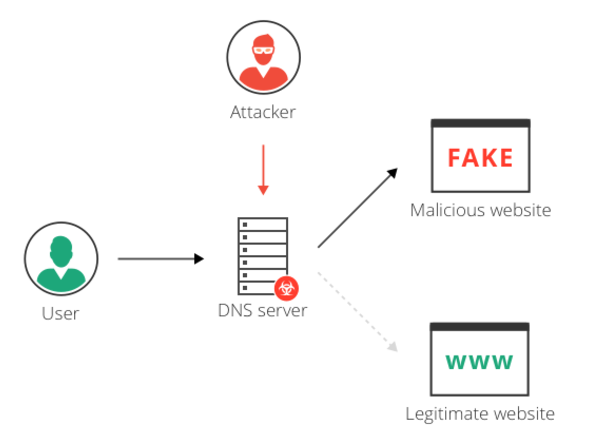
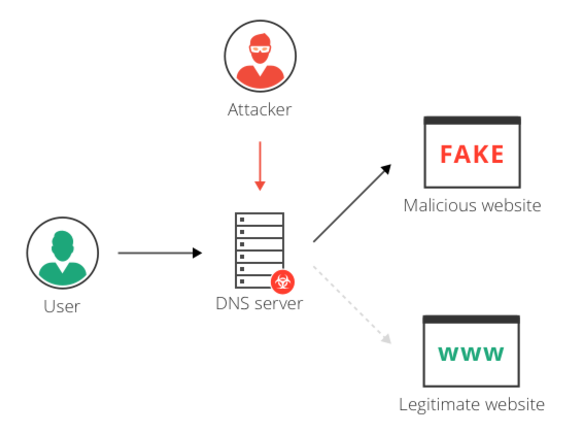
- DNS Hijacking
DNS hijacking is the method of diverting an individual to the doubtful DNS(Domain Name System). It can be achieved by making use of any malicious software or any unauthorised alteration of a server.
The individual has the authority of the DNS. Thus, the individual can be a guide for others who obtain it on a web page. This seems identical, but it carries the extra content very similar to the advertisements.
- How to Prevent?
Here are a few of the prevention methods for DNS hijacking.
- Look for resolvers on your network.
- Restrict access to a name server.
- Make use of measures against cache poisoning.
- Instantly patch known vulnerabilities.
- Segregate the authoritative name server from the resolver.
- Restrain zone alterations.
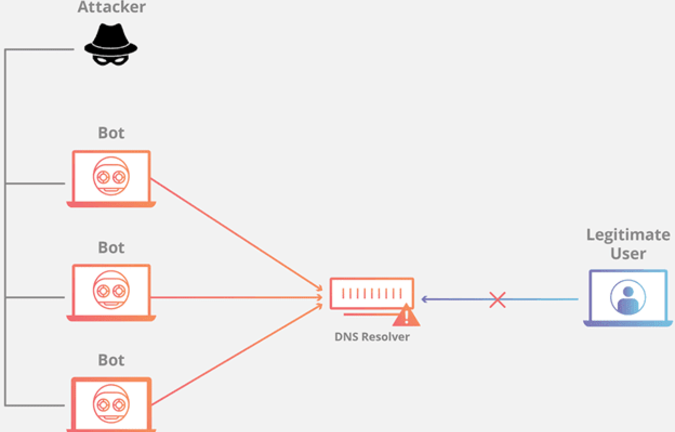
- Phantom Domain Attack
Phantom domain attacks are similar to casual subdomain attacks. Attackers attack the DNS resolver and overpower it. This is done to use the supplies for determining what we name “phantom” domains.
Letting the DNS resolver server await the answer for a long time is the main aim of this DNS attack.

- How to Prevent?
Analyzing the log messages and following the steps below can help in mitigating such attack.
- Increase the number of recursive clients.
- Restrict the recursive queries per server.
- Restrict the recursive inquiries per zone.
- Empower to hold down for non-responsive servers.
- Check recursive queries per zone.
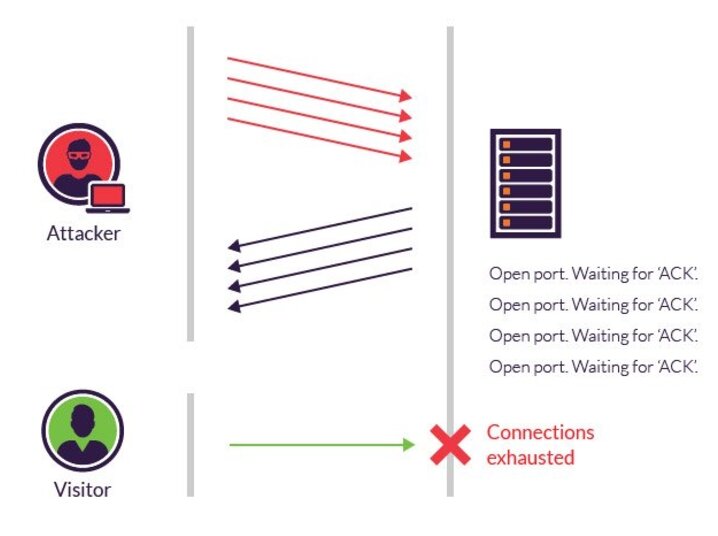
- TCP SYN Floods
TCP SYN Flood is a form of Denial-of-Service (DDoS) attack. It targets the operation related to the internet. It even implements the Transmission Control Protocol (TCP) services.SYN wave is a type of TCP State-Exhaustion attack. It mainly endeavours to utilise the connection element tables.
Such types of attack bring down high-capacity devices connected to manage millions of links. This attack occurs in a situation where the attacker overflows the system with SYN questions. This is done to destroy the target. Also, for making it incapable of reacting to new real connection offers.
Network security, firewalls and IPS devices are insufficient to protect a network from complex DDoS attacks.
- How to Prevent?
More sophisticated attack methodologies are used for attacking the devices. Thus the demand for a multi-faceted program has rosed as it allows users to look beyond both internet foundation and network availability.
- Provide proper support to both inline and out-of-band deployment.
- Extensive network distinctness with the capacity to see and examine traffic from various parts of the network.
- Different sources of threat intelligence, including statistical exception detection, customisable entrance alerts, and fingerprints of known threats that assure fast and reliable detection.
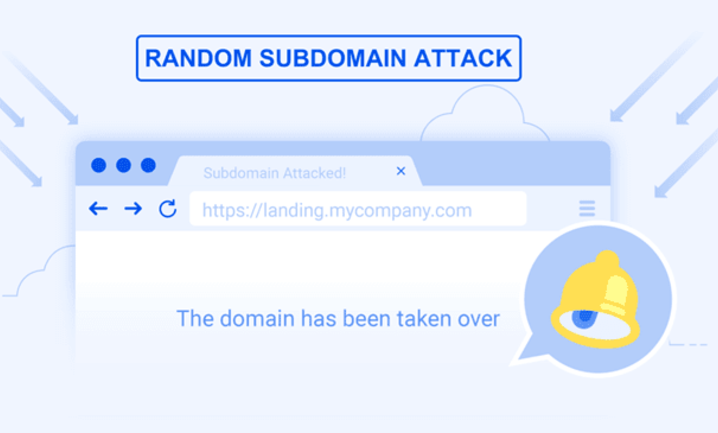
- Random Subdomain Attack
Random subdomain attacks are identified as DoS attacks. The reason being the creation adheres to the same goal as simple DoS. This is not the most prevalent type of DNS attack.
The main motive of this attack is to build a DoS. This would help in immersing the authorized DNS server as it receives the primary domain name. Thus this attack is brutal to identify.
- How to Prevent?
Thus we have provided you with a simple method for preventing the random subdomain attack only in a 30-minute.
- One has to learn the techniques to mitigate the attacks as it generates extreme traffic on resolvers and web resources connected with the victim.
- Learn about modern capabilities like Response Rate Limiting for preserving DNS experts that provoke attacks.
- DNS tunnelling
DNS tunnelling is a cyberattack. It is primarily used for carrying out the encoded data from the different applications present inside DNS acknowledgements and queries.
These systems were formerly not created to attack multitudes. Instead, it was designed to bypass interface controls.
Implementing DNS tunnelling demands for gain entrance to a settled system and access to an internal DNS server, a domain name, and a DNS authoritative server.
- How to Prevent?
Here are a few steps to mitigate such types of attacks.
- Create an access rule.
- Create a protocol object.
- Create an application rule.
- DNS Flood Attack
DNS Flood Attack is a primary type of DNS attacks. In this attack, the Distributed Denial of Service (DDoS), the intruder, hits the DNS servers. Overloading the server entirely is the main objective of this attack.
Attacks of such kind can be revealed quickly as the source comes from one single IP. Such attacks get complicated when it becomes a DDoS.
- How to Prevent?
The periodic stale content update and management of a list of several DNS servers help in preventing such attacks.
- Domain Hijacking
Domain Hijacking involves setting the DNS servers and domain registrar to manage the traffic from actual servers to the new destinations.
It is affected by exploiting the vulnerability in the domain name registrar’s system. However, it can also be performed at the DNS level.
When an attacker hijacks a domain name, it uses it to do the originating malicious movements. This may include installing fake pages of repayment.
- How to Prevent?
To mitigate domain hijacking, the following methods can be practised.
- Upgrade your DNS in the application foundation.
- Use DNSSEC.
- Secure access.
- Client lock.
- Botnet-based Attacks
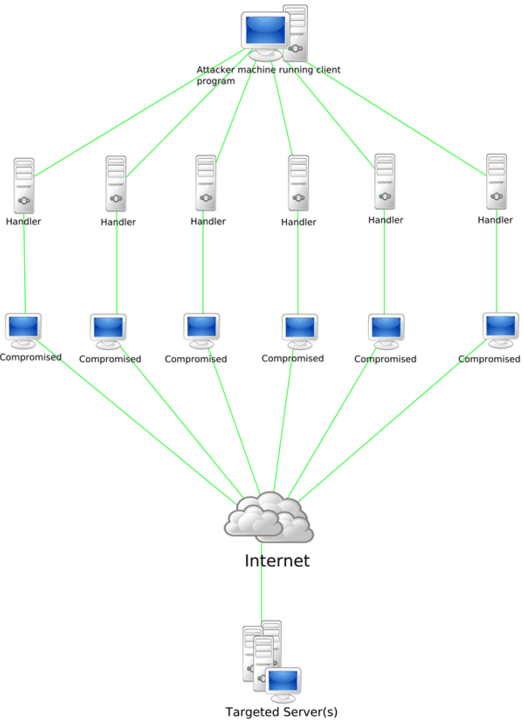
A botnet is some Internet-connected devices. This attack is mainly practised for implementing the distributed denial-of-service attack (DDoS attack). This is done for stealing the data, transmitting spam messages, and doing wicked things.
Botnets are diverse and evolving threats. These attacks are bound to develop parallel, along with growing dependencies on digital devices, the internet, and new future technologies.
- How to Prevent?
The botnet is one of the frequent DNS attacks; to mitigate such attacks, one must follow the below-mentioned steps.
- Understand the vulnerabilities properly.
- Secure the IoT devices.
- Identify both the mitigation myths from facts.
- Discover, classify and control.
So, are you looking for an organisation that provides the best Penetration Testing Service?
If you feel that you have been attacked by one or more of the following malware of the above in your devices, it is best for you to get your network infrastructure penetration testing to be done by the best.
Indian Cyber Security Solutions has been acknowledged as one of the "Top 20 Tech Brands of 2021" by Business Connect India. This has attracted many businessmen from international market to invest in the field of Information Technology. With the improvement in economic development as well as the buying behaviour of the people. With this, the need for reliable network is needed with a proper security services in it. ICSS, aims in providing network security services that is hack free. We work in building a hackproof, secured network infrastructure for your devices.
Why Choose us ?
CYBER INSURANCE – 70% of the project cost will be paid back to the client if any cybersecurity incident is recorded & proved on the same scope of work where ICSS had performed the VAPT.
NON-DISCLOSER AGREEMENT – This agreement states that if any critical data of the client is exposed, tempered or used for any promotional activity without any written consent of the client, ICSS will be held responsible and can be sued in the court of law. ICSS singes NDA with every client before the audit / VAPT.
VA & PT – ICSS performs both VA- Vulnerability Assessment and PT- Penetration Testing for all clients.
ZERO-False Positive Report – ICSS provides manual-based testing along with tool-based testing which reduces the false positive report to maximize accurate identification of critical level vulnerabilities.

- Reference
Source: https://cybersecuritynews.com/dns-attacks/
DOES THIS ARTICLE HELPED YOU?
Stay updated and connected with Indian Cyber Security Solutions. Follow our social Medias (Facebook, Instagram, LinkedIn, YouTube) to get all updated and latest technology related news. We are the largest cybersecurity training & service provider in India. For any query feel free to contact us at 1800-123-500014 or write us at info@indiancybersecuritysolutions.com